So this was a weird one. Remote desktop stopped working on client machines. Troubleshooting led to a group policy Block rule in the Windows firewall but there was no such GPO setting.
TLDR: Don’t put any spaces in the IP address list for the GPO setting for Computer/Admin Templates/Network/Network Connections/Windows Firewall/Domain Profile/Windows Firewall: Allow inbound Remote Desktop exceptions.
After adding a subnet to the “Windows Firewall: Allow inbound Remote Desktop exceptions” Remote Desktop stopped working.
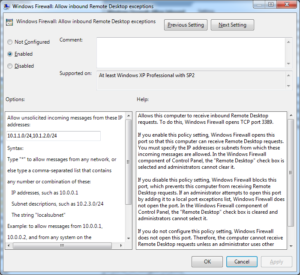
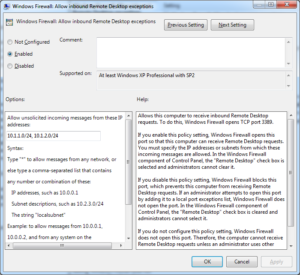
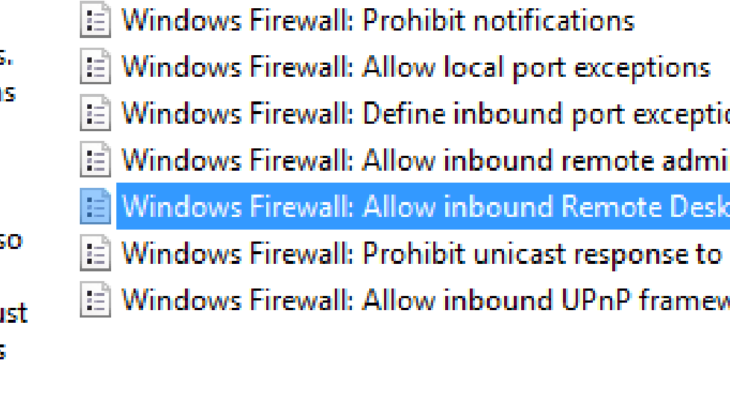
This is the policy…
And this is the setting applied adding a second subnet into the Allow unsolicited incoming messages from these IP addresses…
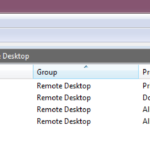
After troubleshooting I found the cause was the firewall rule on the local machine was now set to “Block”.
The rule couldn’t be deleted because this rule has been applied by the system administrator and cannot be modified. In other words it was set by a GPO.
The group policy results tool showed no block rules for remote desktop and only the Allow inbound Remote Desktop exceptions shown above. After trying all the common sense tests I removed the second IP address from the policy… and after a GPUPDATE the firewall rule changed back to Allow….
This was unexpected…. so I added the second address in again and the rule changed back to “Block”.
As a further test I changed the rule to an allow all “*” which also worked correctly setting the rule to “Allow”.
On a hunch I added both subnets back in and removed the “good formatting” space between them… and the rule worked properly and set to allow.
So adding a space into the Allow unsolicited incoming messages from these IP addresses converts the policy from Allow to Block. Weird.
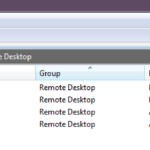
Works! |
Doesn’t Work. |
 |
 |










Thanks for posting this solution – I had the exact same thing occuring. This saved me at least 3 grey hairs.
Removing the leading and trailing spaces around the comma solved my issue as well
Thanks – this helped me with a weird set of NETBIOS rules on a server that were set to BLOCK but I could not find their source! Taking the spaces out of a firewall related list in GPO object fixed this!
Thanks!
Great content! Super high-quality! Keep it up! 🙂
Wow! Fixed me right up…Appreciate it
Helped me so much, thank you! Was driving me crazy trying to figure out where the setting was being applied from.
天有不测,及时享乐!